- Qualcomm Launches Snapdragon 4 Gen 2 Mobile Platform
- AMD Launches Ryzen PRO 7000 Series Mobile & Desktop Platform
- Intel Launches Sleek Single-Slot Arc Pro A60 Workstation Graphics Card
- NVIDIA Announces Latest Ada Lovelace Additions: GeForce RTX 4060 Ti & RTX 4060
- Maxon Redshift With AMD Radeon GPU Rendering Support Now Available
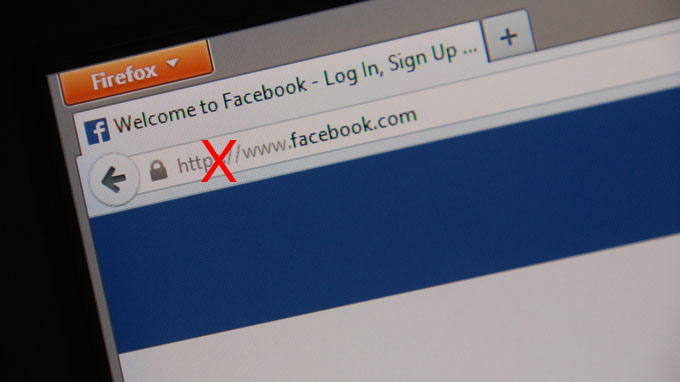
There is Only One Internet
The press coverage for Heartbleed has come and gone, and it seems like the public has missed the message. Brett takes a step back to glance at the bigger picture of a world that authenticates based on what we know, and what that means when everyone else knows it, too.
So, are you sick of hearing about Heartbleed yet? Sure, I bet you are. It’s ok, you’re not the only one – the coverage has exhausted me, and I love information security. After reading, seeing and hearing story after story from the major media outlets all the way from CNN to NPR, two things are for sure – your secrets are probably out there, and most people outside of the technorati still don’t know why it matters.
Being a huge security nut, I’ve had more than a couple of people ask me about the Heartbleed vulnerability – what sites it’s affected, what kinds of information it could have given up. Through multiple discussions with people of multiple backgrounds, I’ve come to realize that the media probably should stop talking about it: The explanations by most mainstream outlets has made people less aware of the ramifications, not more. Reporters talk about it like it was an attack by hackers, which does a tremendous disservice as we can’t say what data was stolen, by whom and from where. It quickly went from the most pivotal threat of our digital age to background noise.
A big part of this can be credited to the fact that it was patched in a virtual instant. This extremely timely response can be considered a gold star for the open-source community, which immediately began submitting code changes to the SSL standard. I’d hate to think of what might have been if this were a privately owned piece of software with no public scrutiny of the source, like Windows or OS X.
Read the rest of our article.