- Qualcomm Launches Snapdragon 4 Gen 2 Mobile Platform
- AMD Launches Ryzen PRO 7000 Series Mobile & Desktop Platform
- Intel Launches Sleek Single-Slot Arc Pro A60 Workstation Graphics Card
- NVIDIA Announces Latest Ada Lovelace Additions: GeForce RTX 4060 Ti & RTX 4060
- Maxon Redshift With AMD Radeon GPU Rendering Support Now Available
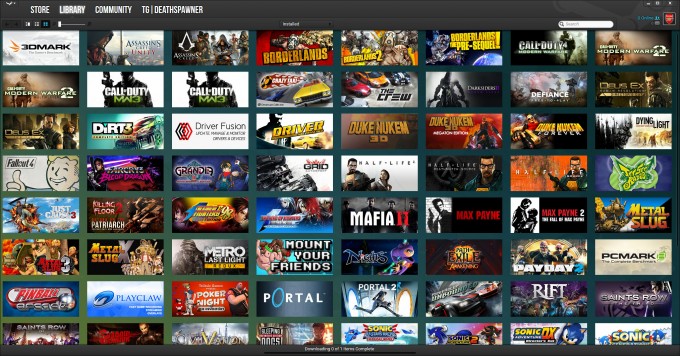
Valve Details Steam-crippling Christmas Day Issue
On Christmas Day, one where many people would have been on Steam to cash in gift cards, the service experienced one heck of a screw-up. Between 11:50AM PST and 13:20PM PST, a huge number of users experienced an odd phenomenon where on a page refresh, a page destined for someone else was seen. From there, if a user went to the account details page, that other user’s information could be seen, which included billing address, purchase history, and even wallet sizes.
For many Steam users, the most frustrating thing about this whole episode is how long it took Valve to take the site down to fix the problem. 90 minutes is a long time for something like this, and ultimately, it resulted in 34,000 accounts becoming exposed. Fueling fury further, Valve has kept largely mum on the issue as it sorted through the details. Fortunately, an update finally came yesterday.
On the day of the debacle, Valve said that the issue was cache-related, and this latest post reaffirms that. While the company is not name-dropping the caching service it uses, the problem overall was caused by a simple configuration error. Why that came about is simple: Valve had to beef-up its caching solution due to the fact that Steam was getting hit hard with a DDoS attack. The post notes that during the attack, the site experienced 2000% more traffic over the average during a Steam sale. So while the DDoS itself isn’t what caused this to happen, it led to this mistake happening.
The risk to exposed users is very low, as truly important information was left secured. Only the final 2 digits of exposed user credit cards were revealed, and the final four digits of their phone number. Still, this is not a great thing to happen, and once Valve figures out who those 34,000 users were, they will be reached-out to.
This needs to be a lesson to any company that offers online services; a mere caching configuration issue can really ruin your day.