- Qualcomm Launches Snapdragon 4 Gen 2 Mobile Platform
- AMD Launches Ryzen PRO 7000 Series Mobile & Desktop Platform
- Intel Launches Sleek Single-Slot Arc Pro A60 Workstation Graphics Card
- NVIDIA Announces Latest Ada Lovelace Additions: GeForce RTX 4060 Ti & RTX 4060
- Maxon Redshift With AMD Radeon GPU Rendering Support Now Available
TrueCrypt Primer: Part 1 – What It Is & Why You Should Care

We’ve talked a lot in the past about keeping your computer safe and data backed-up, but we haven’t delved much into keeping your data secure. In this first part to a three-part series, we’re taking a look at one of the best (and easiest-to-use) cross-platform solutions for keeping your important data encrypted: TrueCrypt.
Page 4 – TrueCrypt Trustworthiness
It is not just the encryption algorithms and overall security measures being used that should be under the watchful eye of anyone committed to securing their data. We provide a modicum amount of security to our daily lives by making use of a small network of trust. We tell a friend a secret if we trust them to keep it, we allow a director to write checks from our business account if we trust them to be honest. Likewise, we generally entrust our personal data to websites or services on a basis of trust.
TrueCrypt itself is not a security measure. It is a tool that implements a security measure. This distinction is important and because of it, it should be under close scrutiny. Does TrueCrypt do what its authors say it does? Does it have any backdoors? What are other people saying about TrueCrypt? Has it been broken before? Has anyone analysed TrueCrypt in any detail? Who makes TrueCrypt?
These questions make sense when we want to entrust TrueCrypt to secure our most sensitive data and no one should feel intimidated to ask them.
As you can expect, TrueCrypt has been under the scope of many a user. Through the years, some arguments have surfaced questioning TrueCrypt as a safe tool. Note that this is perfectly acceptable. From a security point-of-view, reports on the strengths of a security tool are mostly anecdotal and usually of little value. There’s good reason to keep a cynical mind about these matters, and want only to pay attention to that which may be revealing of its weaknesses. But an inquisitive and cynical mind isn’t enough. One should also remain rational and pass any information through the filter of common sense.
One such place that lists the security issues that some users have been pointing out is found on a personal blog: Privacy Lover. Here you will find the top concerns regarding TrueCrypt trustworthiness. Before reaching the end of this first article on TrueCrypt, I’d like to address a few of them myself:
Nobody knows anything about the developers, they do not want to identify themselves.
This is indeed troubling. It’s hard to imagine why the TrueCrypt developers wish to remain anonymous. There may be personal reasons we can’t be aware of, but in the face of it, one would expect (given the nature of the tool) the developers to be more open-minded about this issue and simply state — not the actual reasons — but their motivation to remain anonymous.
Closed source full disk encryption competitors like WinMagic, DriveCrypt (Securstar) and PGP Corporation have a full time team of software developers working in their products[…] meanwhile two unpaid TrueCrypt developers manage to work on Linux, MAC and Windows versions, on 32 and 64 versions and support the next Windows 7 as soon as it has been released, at the same time, presumably, these two TrueCrypt developers also hold full time jobs that pays them a salary to feed their families and covers their mortgages.
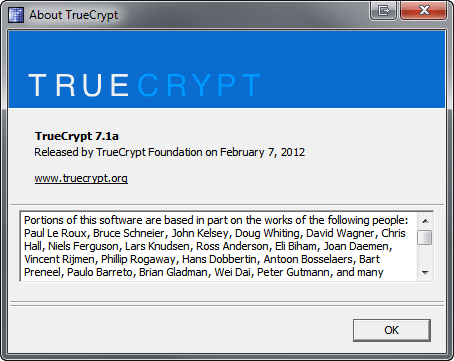
This is entirely incorrect. TrueCrypt has been under development since at least 2002. Its early versions were nothing like what we see today and it can be safely said TrueCrypt is a work in progress that has been constantly built upon the foundations of its earlier versions. Furthermore, TrueCrypt is based on well-known and publicly available algorithms and encryption methodologies the authors didn’t invent. The application complexity is evident. But a large part of this isn’t credited to TrueCrypt authors. The application’s About Dialog Box lists a good number of people that directly or indirectly contributed to TrueCrypt development.
Meanwhile, there shouldn’t be a need to mention the tremendous contribution other solo developers have been giving to computer science and tooling in particular. The simple matter of fact is that there are passionate and dedicated individuals in this field that will reserve a large part of their lives for the pleasure of creating something truly useful to themselves and to others.
TrueCrypt’s source code has never been the subject of a thorough review.
This is speculative at best. There’s no reason to believe such is the case. Those interested in doing so (namely governments and large companies) do not usually publish the results of their findings, nor it is in their best interest to divulge what security measures they are using or which ones they have tested. But I’ll be speculating too if I keep on that line of reasoning. What’s perhaps more important to note is that the full source code is made available and can be compiled into a working executable. Regardless of how we analyse the issue of peer review, I’d be hard-pressed to believe the source code contained any backdoors; which would immediately stand out to any qualified reviewer.
As per TrueCrypt forum rule 3 you are not allowed to discuss about other encryption software, as per TrueCrypt forum rule 8 you can’t discuss TrueCrypt forks, as per TrueCrypt forum rule 9 you can’t discuss software that decrypts Truecrypt.
This falls flat in the face of a project the developers call open source (it isn’t for various reasons, but they call it such). It is indeed troubling that the software can’t be openly discussed. However this is simply an administrative decision. There’s nothing stopping anyone from discussing it on some other place on the Web, possibly with a lot more visibility than the TrueCrypt forums. It didn’t stop, for instance, Peter Kleissner from developing the Stoned MBR rootkit — which under certain conditions is capable of bypassing TrueCrypt’s Windows system encryption — and speak about his results at the most prestigious computer security conference on the planet.
I’m going to conclude this first article on TrueCrypt by noting that this is not a tool you should consider trustworthy. It’s like beating a dead horse, saying that no tool offers complete security or trust. But the real meaning of this sentence is often lost. What is important to keep in mind is that we should make realistic concessions based on who we are and what type of information we want to hide. Assuming some agency like the CIA (or your local flavor of a secret service agency) has access to a backdoor on TrueCrypt, it is very unlikely they would blow the lid on it because of someone hiding embarrassing pictures, pirated music or the plans for a more efficient combustion engine.
On a comical note, according to a certain Brazilian banker it may be good enough to hold data that contains all your corrupt activities. You may work from that baseline.
Support our efforts! With ad revenue at an all-time low for written websites, we're relying more than ever on reader support to help us continue putting so much effort into this type of content. You can support us by becoming a Patron, or by using our Amazon shopping affiliate links listed through our articles. Thanks for your support!




