- Qualcomm Launches Snapdragon 4 Gen 2 Mobile Platform
- AMD Launches Ryzen PRO 7000 Series Mobile & Desktop Platform
- Intel Launches Sleek Single-Slot Arc Pro A60 Workstation Graphics Card
- NVIDIA Announces Latest Ada Lovelace Additions: GeForce RTX 4060 Ti & RTX 4060
- Maxon Redshift With AMD Radeon GPU Rendering Support Now Available
Latest Articles
-
Home
> Security
-
A Problem With Jaxx Cryptocurrency Wallet Security
Jumping into the cryptocurrency world can feel overwhelming; there’s a lot to learn, and unfortunately, some lessons come late. Sometimes, it can be due to not knowing what you’re doing, but other times, weak security is to blame. We’re going to explore an example of the latter here, with the help of our formally favorite crypto wallet.
February 19, 2018 | Rob Williams | Editorials & Interviews, Security -
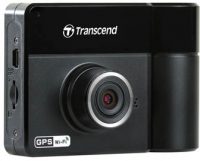
A Road Trip With The Transcend DrivePro 520 Dashcam
The DrivePro 520 is a full-featured dashcam that has it all. With dual cameras, low light usage, infrared, GPS, mic, and a battery, this cam targets the full range of professional drivers from commercial haulers, passenger carriers, or just business vehicles. It also offers a proper toolkit for parents, so whatever your needs, Transcend’s DrivePro 520 can probably exceed them.
April 27, 2017 | Robert Tanner | Peripherals, Security -
Addonics CipherUSB Review – Portable Encryption Made Easy
As important as data encryption can be for the home user, it’s even more imperative in the enterprise. The problem? The most effective measures are usually cast aside in lieu of something a little easier to deal with. With the CipherUSB, Addonics hopes to bring “simple” and “most effective” together as one. Does it succeed?
July 3, 2013 | Brett Thomas | Security, Storage -
SysAdmin Corner: Introduction to Pentesting and the Pwn Plug – Part 1
Many sysadmins understand how to set up and maintain a network, but the concept of auditing is an entirely different world. In the first part of a series on auditing and penetration testing (pentesting), we introduce the concepts and tools for putting all that security to the test. We’ll also talk about our pentest platform of choice, the Pwn Plug.
December 20, 2012 | Brett Thomas | Editorials & Interviews, Security -
TrueCrypt Primer: Part 1 – What It Is & Why You Should Care
We’ve talked a lot in the past about keeping your computer safe and data backed-up, but we haven’t delved much into keeping your data secure. In this first part to a three-part series, we’re taking a look at one of the best (and easiest-to-use) cross-platform solutions for keeping your important data encrypted: TrueCrypt.
November 20, 2012 | Mario Figueiredo | Editorials & Interviews, Security -
SysAdmin Corner: 7 Network Security F-Ups Small Offices Make
It’s easy to overlook that huge corporations are far less dangerous than the small business you deal with each and every day with regards to information theft. Some institutions have treasure troves of info on you that can far exceed the “big fish”. If you work in a SMB, you can’t afford to have your info stolen, so read on for some important tips.
October 19, 2012 | Brett Thomas | Editorials & Interviews, Security -
VPS: What It Is and How It’s Useful
We’ve talked a fair bit about home virtualization in the past, but now we’re going to take a different turn and tackle VPSs, or “Virtual Private Servers”. In essence, a VPS is a virtual machine in the cloud, allowing you to log in from anywhere and gain nearly full control over a remote machine with tons of bandwidth to do a variety of cool things.
December 3, 2010 | Rob Williams | Security, Software -
Super Talent SuperCrypt 32GB USB 3.0 Flash Drive
With USB 3.0 storage devices popping up all over, now is a good time to consider making the move to one, whether it be an enclosure or flash drive. To kick off what will be the first of many USB 3.0 device reviews, we’re taking a look at Super Talent’s SuperCrypt thumb drive, which promises both huge speeds and huge data protection.
June 9, 2010 | Rob Williams | Security, Storage -
Too TRIM? When SSD Data Recovery is Impossible
It goes without saying that solid-state drives are well-worth the investment in order to give your PC some responsiveness, but with all the benefits they can offer, there’s one lesser-known issue that we’ll talk about here. That issue is simple. As soon as you delete a file on a TRIM-enabled SSD, the data is gone, for good.
March 5, 2010 | Rob Williams | Security, Storage -
Addonics CipherChain Hard Drive Encryption
We took a look last week at a thumb drive that offered unparalleled data security, and this time around, we’re taking a look at a similar product, but one that’s designed for PC use, whether in the office or at home. The CipherChain, from Addonics, is easy-to-install and operate, and secures your data using the ultra-secure AES 256-bit cipher.
December 9, 2009 | Rob Williams | Security, Storage -
Quick-Gage: Kingston 16GB DataTraveler Locker+
It may seem like a given that personal data should be kept secure, and for the most part, achieving that goal on a home PC isn’t too difficult. But, what about a thumb drive? Kingston’s DataTraveler Locker+ is designed in such a way that if someone ever finds your thumb drive, they’ll never be able to access the data. Ever.
December 2, 2009 | Rob Williams | Security, Storage -
Steganos LockNote 1.0
Do you like the simplicity of Notepad, but want the security of Steganos? That’s where LockNote comes in to play, which protects your text with 256-Bit encryption. This is also the very first Steganos product to be labeled as freeware, and it’s even open source!
January 26, 2006 | Rob Williams | Security, Software -
Steganos Security Suite 2006
Steganos cares about your computer security, and offers a complete suite to make sure you are kept safe. It combines 10 security tools together into one massive package, and we are going to take a look at what’s available and see if it’s worth your money.
December 14, 2005 | Rob Williams | Security, Software -
Steganos Internet Anonym 2006
Steganos have just released a new version of their award winning Internet Anonym program, which brings us to version 8! We are taking a look at the basics, and also what’s new. Has much changed? Let’s check it out.
September 16, 2005 | Rob Williams | Security, Software -
Internet Anonymity – Anonymizer vs Steganos
Last week, we took a look at what Internet Anonymity is, and how it works. Today, we will be taking a hard look at two of the most popular Anonymity tools out there.
August 8, 2005 | Rob Williams | Security, Software
| Title | Author | Date | Categories |
|---|---|---|---|
| Internet Anonymity – How you can stay safe online | Rob Williams | August 3, 2005 | Security, Software |