- Qualcomm Launches Snapdragon 4 Gen 2 Mobile Platform
- AMD Launches Ryzen PRO 7000 Series Mobile & Desktop Platform
- Intel Launches Sleek Single-Slot Arc Pro A60 Workstation Graphics Card
- NVIDIA Announces Latest Ada Lovelace Additions: GeForce RTX 4060 Ti & RTX 4060
- Maxon Redshift With AMD Radeon GPU Rendering Support Now Available
TrueCrypt Primer: Part 1 – What It Is & Why You Should Care

We’ve talked a lot in the past about keeping your computer safe and data backed-up, but we haven’t delved much into keeping your data secure. In this first part to a three-part series, we’re taking a look at one of the best (and easiest-to-use) cross-platform solutions for keeping your important data encrypted: TrueCrypt.
Page 1 – Introduction
Data has never been such a traveler. In our mobile devices, flash drives, computer desktops, on the Internet and in the multitude of cloud services, data is constantly being downloaded, uploaded, or synced. Data that we have generated ourselves – like a spreadsheet for a financial report, work we brought home from the office, our photo albums and more. If something has to be said about data these days, it’s that never before has data security been such an important consideration for humankind.
We’ve been experiencing the Internet through the filter of user names and passwords. Almost anywhere we go we are required to sign up for a new account, or sign in to an existing one if we have been there before and have already left our credentials stored on the website or Web database. But if passwords and usernames offer some amount of security, it’s just a modicum dose. I would go as far to argue that passwords aren’t a security measure at all; they are data like any other that needs to be secured and merely offers an authentication method to an in-place security measure.
As such, true security derives from how we store the actual data, including passwords. In modern times this has become an absolute imperative and anyone using the Internet should at one time or another become familiar with any security measures to protect their data. Encryption is one such measure and the most widespread.
A General Look at TrueCrypt
In this three-part series, we are going to take a deep look at TrueCrypt. TrueCrypt is a free software tool that’s been developed since 2004 and is made available by the TrueCrypt Foundation. With this tool it is possible to create a virtual encrypted disk within a file, or encrypt a partition. Under Windows it is also possible to encrypt the entire boot drive.
As of this writing, TrueCrypt’s latest version is 7.1a. The three articles in this series will refer to this version. TrueCrypt is available for Windows, Linux and MacOs X operating systems — but what you can do with it depends on the type and version of your operating system.
| Virtual Disks | Partition Encryption | System Encryption | |
| Windows 8 (32 & 64 bits) 1 | Yes | No | |
| Windows 7 (32 & 64 bits) | Yes | Yes | |
| Windows Vista (32 & 64 bits) 2 | Yes | Yes | |
| Windows XP (32 & 64 bits) | Yes | Yes | |
| Windows Server 2008 R2 | Yes | Yes | |
| Windows Server 2008 (32 & 64 bits) | Yes | Yes | |
| Windows Server 2003 (32 & 64 bits) | Yes | Yes | |
| Mac OS X 10.7 Lion (32 & 64 bit) | Yes | No | |
| Mac OS X 10.6 Snow Leopard (32 bits) 3 | Yes | No | |
| Mac OS X 10.5 Leopard (32 bits) 3 | Yes | No | |
| Mac OS X 10.4 Tiger (32 bits only) | Yes | No | |
| Linux Kernel 2.6 or compatible (32 & 64 bits) | Yes | No | |
1 The TrueCrypt website makes it clear Windows 8 isn’t fully supported yet. Despite any success you might have encrypting a Windows 8 system partition, this is not recommended until full Windows 8 support is given on a future version of TrueCrypt.
2 System partition encryption is only possible with Windows Vista SP1 or above.
3 64 bit support can be obtained by installing OSXFUSE.
You can see from the table above that Linux-based systems don’t support system encryption. This is due to the OS design. Such a feature would have to be able to handle Linux-supported filesystems (at least the most widely used ext3, ext4, etc). It would also need to support more than one bootloader and be intelligent not to destroy their rules when placing its own. It would also need to locate and encrypt the distinct swap volume. While doable, the amount of work required may mean TrueCrypt will never provide support for Linux system encryption.
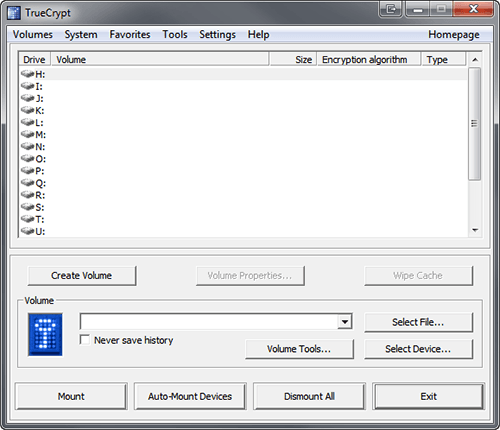
TrueCrypt main window
TrueCrypt supports the following encryption algorithms:
In addition, TrueCrypt supports Multiple Encryption. This technique (also known as Cascade) encrypts data using multiple encryption algorithms in succession. (The file is first encrypted with one algorithm, and then another encryption takes place on top of the previous one with another algorithm).
The supported Cascades are:
- Serpent-AES
- Twofish-Serpent
- AES-Twofish-Serpent
- Serpent-TwoFish-AES
The cryptographic hash algorithms supported by TrueCrypt are:
Algorithms and hash functions will be discussed in more detail on the second part of this series.
Support our efforts! With ad revenue at an all-time low for written websites, we're relying more than ever on reader support to help us continue putting so much effort into this type of content. You can support us by becoming a Patron, or by using our Amazon shopping affiliate links listed through our articles. Thanks for your support!